You are working tirelessly on a research project for few months now, which is a week away from deadline. The most horrifying thing happened – “a computer virus causes your file to be corrupted!”.
Wanna learn some interesting facts about computer viruses like why are there computer viruses and more? The risk of computer viruses is closely similar to the more popular kind, the human viruses. Both are destructive and harmful which destroys hosts. Once a computer is infected with virus, a portion of software halts or messes the device’s functions. But there are more surprising things you did not know about computer viruses. Here are the:
25 Things You Didn’t Know About Computer Viruses:
#1 The first ever computer virus was a computer worm

Computer programs and the internet (which was originally known as the ARPANET) are developed for military network defense purposes. Based on records, the Creeper virus is the first ever computer virus.
It is a self-replicating virus that display words, “I’m the creeper, catch me if you can”, which started at US military’s DEC PDP-10 and spreads throughout nearby connected units in early 1970’s. This kind of behavior of virus is considered now as computer worm. Like any other science experiment gone bad, Thomas Bob did not intend to create a worm but was trying out codes that would later be applicable to mobile apps in early 1970’s.
#2 Creeper is the first ever anti-virus software

In response to the accidental creation of the first virus, the first ever anti-virus “Creeper” was programmed. Probably the team of computer programmers may giggle while they advise office computer user to, “You got to install Creeper to clean the Reaper”.
#3 One for the earliest virus is used to prank friends

Yes, you read it right. In 1982, 15-year-old Rich Skrenta, played with codes with the intention to trick friends. The code contains a poem he entitled “Elk Cloner: The Program with a Personality”. His plan was to display it to the blank screen of the game he and his friends play. Unfortunately, the floppy disc used has infected other discs inserted in the same computer. Thus, transferring the virus to other computers.
Photo from “Pixabay”
Elk Cloner virus creator became a successful businessman and programmer later in his life.
#4 Evolution of computer virus is oppositely different from human Virus
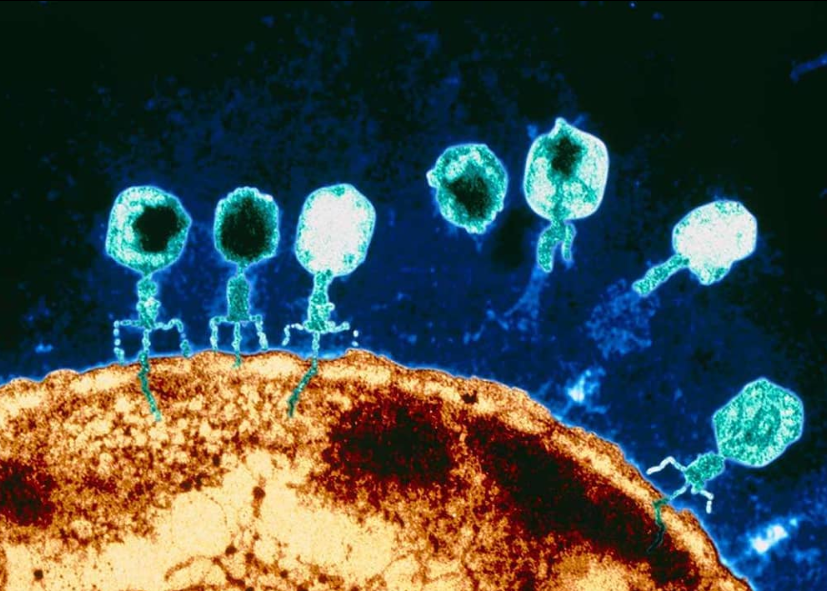
Although the two has the same intent to infect hosts, both originate from different ways. Human virus has unsure evolution which hypothetically believed as an independent particle or a progression from bacteria. The other, computer virus is intentionally created to serve its purpose to destroy.
#5 Computer bugs are not viruses

Bugs are often mistaken as a type of virus. Computer bugs are program errors made by programmers. However, there are virus that are directly outcome of coding mishaps. Bug is a result of a faulty performance due to badly written or incorrect syntax from a software’s code. Virus, on the other hand, is a software itself that is programmed to cause other software to malfunction.
#6 Difference between computer viruses and worms

Computer worms are as destructive as virus do. There are viruses that behave like worms replicating itself to cause damage. However, worms are malware that does not infect other device contrary to viruses behavior.
#7 Connection between virus and Trojan

rona_ronskie
Trojan is a malware which masks as another software. Trojan is from the infamous Greek Trojan Horse used to infiltrate and defeat Troy. Like virus and worms, Trojan is equally destructive which displaying annoying pop ups, and opens backdoor for other malware to access to. Yet, worms and (some) virus replicates but not Trojan. When Trojan infects other devices, it becomes a virus.
#8 One of fastest spreading virus is the ILoveYou virus

In the year 2000, email became popular that it became a commodity like social media today. People back then enjoyed the pleasure of sending and receiving sweet messages through anonymous digital letters. The vulnerability of people to open files from secret admirers have caused the self-replicating ILOVEYOU virus to leave $10B damages overnight. Even US senators have fallen into trap of opening e-mails that have “SUBJECT: I Love You”, thus spreading it faster.
ILOVEYOU virus is an altered code from the Melissa virus which also replicate the word “I Love You.” However, the ILOVEYOU virus overtakes the host’s register key, then send the infected email to all contact its list.
#9 Mydoom virus left the most expensive damages

Few years after the infamous ILOVEYOU virus, the Mydoom has carried about $38.5B of damages. The virus spread quickly through email that send multiple attachment spams. The virus is a malware that leaves computer backdoor open, making internet speed slower.
#10 Computer virus is used as a spy tool

A spyware is a type of virus that collects data from infected device, causes a security threat. Last 2018, an unnamed virus is feared to have tapped and infected Iran’s President Hassan Rouhani. It is believed to be “more violent, more advanced and more sophisticated,” compared to the infamous Stuxnet virus.
#11 Computer virus used by hackers to bypass manufacturer computer restriction

Computer developers intend to strictly lock and secure backdoor operating system to prevent exploitation of entry from malicious software. Hackers use this malware like rootkits virus to bypass restriction to several reasons like password, licenses, configuration, and compatibility.
#12 Computer virus used for mass production

Malware bots are virus that produce bot networks which controls the portions of computer’s internal structure. Bots are used by telemarketers and individuals who wants to hasten repetitive tasks like auto generation of security captions, system applications, and data gathering. Though it sounded productive and helpful but oftentimes it is deemed unethical when it bypasses security in computer system.
#13 Computer virus used to mine cryptocurrencies

Torrent websites like Pirate Bay uses bot viruses for its ads from inorganic cash flow. Some fraud companies install crypoto-jacking malware to pages to infect those who access their site and secretly mine cryptocurrency information.
#14 Some businesses exploit virus for marketing ploy

A lot of companies exploit the use of adware which allows marketing advantage across the globe. Bots are viruses capable to send spam mails, unwanted pop-up windows, and networked auto-message messages.
#15 Computer Virus used by aggressors for revenge, and competition leaving no trace

Viruses are often used as tiny robots to interfere with the normal functions of computers. These type of malware can hide IP addresses, make anonymous transactions, and phis personal information that can be used for fraud and harass.
#16 Computer virus damages and losses are too costly

If almost all malware damages were to sum up, it may have reach more the $200B or more! MyDoom and SoBig viruses has combined damages estimated to $80B.
#17 Antivirus companies’ revenue is over $30B

According to data gathered by Statistita security software companies like AVAST, McAfee, Kaspersky Lab, and among others are able to generate a massive worldwide revenue of $32.1B in 2017 and is still increasing rapidly.
#18 Some virus name came from attempt to be funny

Software developers tries to put humor into naming software with conventional odd rhymes or irrelevant origin.
One example was the famous the Code Red virus which puts down thousands of servers. One of the discoverer of the virus was drinking Code Red Mountain Dew, thus randomly naming it as Code Red virus. Some virus came from famous renaissance artists like Michelangelo because it was discovered on the painter’s birthday. Another strange name is Melissa virus from a stripper whom the discoverer met in Florida.
#19 A computer virus cannot infect hardware
Virus are malicious program that attack and cause undesirable activity inside computer’s software, thus cannot directly harm the tangible part of computer. Although, technically hardware resides in hardware part but the issues caused by virus are the codes affecting the software installed inside the device. If CPU does not work or slows down, it was probably caused by virus affecting the operating system. Unless it is physically scratched.
#20 Computer virus is one type of malware

Different types of malware: worm, virus, and Trojan. Virus has the ability to do what worms do but it is able to infect other devices.
#21 Different behaviour of viruses

These are boot sector virus (attacks as computers are turned-on), browser hijacker virus (messes browser settings), direct action virus (needs trigger to activate), file infector virus (resides in operating system and system files), macro virus (attached in files like documents), multipartite virus (infect system sector and spread many ways), polymorphic virus (manipulates codes which is able to bypass antivirus), resident virus (control system memory), and web scripting virus (targets browser and web page functions).
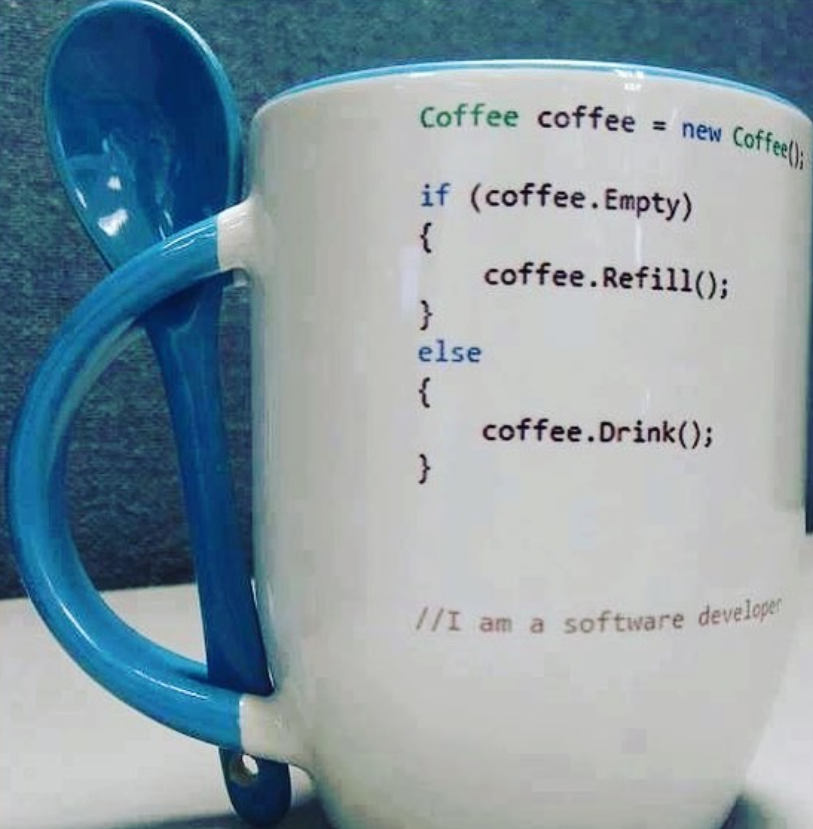
#22 Computer virus is a result of a mix of a genius and a sly mind
Malwares like virus do not just appear from nowhere. Just when you thought that these are done by random dumb programmer whose sole purpose to make device owners’ life miserable – no, they are not!
Shocked? Computer Viruses are series of well thought code combinations that is programmed to infect devices to milk computer and smartphone users. They sell anti-virus software or provide paid services to fix malfunctioning device which were infected deliberately. One may not need a four-year-degree-diploma to create such malware but anyone with logical thinking, strategic capabilities (more like conning skills), and self-learning abilities.
This is like swindling bakers by stealing bread and selling it back to them as cookies.
#23 Monopoly for multi-billion business Anti-Virus Software

Like small time computer virus scammers, there are conspiracy theories that huge successful Software companies are guilty of this scamming scheme. Developing viruses to guarantee endless demand for upgraded and newly released anti-virus software.
Legitimate software companies are cashing-in loads of revenue from the computers and smartphones’ mandate for protection and cure to/from existing viruses, as theorize from members of different online forums questions.
#24 Virus protection and removal

There are many ways to be protected from viruses. Invest on updated anti-virus, practice regular virus scan and disc cleanup, and deleting temporary files. Be cautions of external files, USB storage devices, and other hardware that carry malware. Also, be watchful of internet sites you visit because some pages deliberately spread viruses. Never accept invites and messages from unknown and doubtful sources.
#25 Viruses can be created through any kind of software
Creating computer viruses does not need low level programming language to be coded tediously. Some viruses are coded from the simplest fourth generation languages like Visual Basic or Perl. You will be surprised, clever hackers used Excel Office software to manipulate confidential computer document files.

Cool Article
Quite interesting facts. Seems you researched well
Thanks for the thoughts you reveal through this site.
Currently it looks like Movable Type is the preferred blogging platform available right now. (from what I’ve read) Is that what you are using on your blog?
I am often confused with worms, virus, and malware